Reverse Email Lookup
Owner Name, Address, Phone Number, Social Accounts, Public Records & More!
What Information is Available Through Email Search?

Owner Info
Discover who owns the email address that keeps sending you unsolicited communication or messages, along with basic background information about their Identity, Residence, Education, Employment History, Marital Status and more.

Contact Info
Find out sender’s associated Phone Numbers, Hidden Email Addresses, Current Mailing Address and Previous Residences with just a few clicks. Within seconds our lookup tool will provide the basic personal data behind any e-mail address.

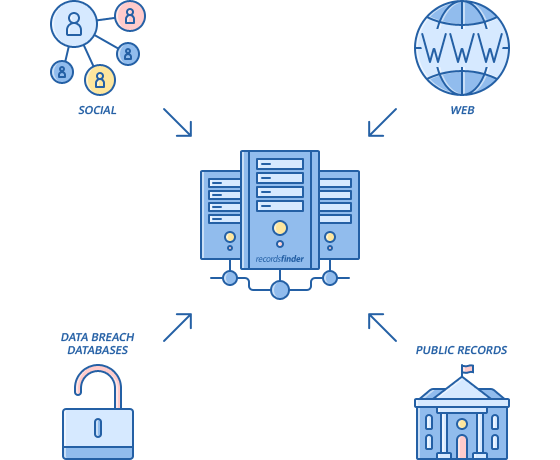
Social Accounts
Trace for their Social, Dating, Professional and other types of Online Networking Profiles, both hidden and official ones. Anyone’s online social activity is a few seconds away. Just try our quick lookup tool and you’ll no longer have to worry.

Web Activity
Is someone keeping a daily blog? Are they avid vloggers or instagrammers? This is the best way to find out. Use our efficient search tool and you get to see their internet footprint, including Forums Posts, Websites, Blogs, Images and Videos.

Data Breaches
Discover if an email address has been breached, whether and when its password has been leaked. Use our intelligent lookup tool to systematically monitor the dark web and check if your data has been stolen. Protect your private data with a few clicks.

Public Records
Search Criminal Records, Arrests, Traffic Violations, Court Records, Marriages, Divorces, Assets and more, online. Access information anonymously, from your favorite devices, without wasting any time with paperwork or waiting in line at public institutions.
What is a Reverse Email Lookup?
A reverse email lookup is a search technique used to find people by their email address. The email address is run through millions of public and private web sources until it finds any potential matches. This type of anonymous search is conducted to reveal the identity of the owner and uncover as much information as possible about them, without them knowing.
Reverse email search will help you identify fake Social Media Accounts, False Names, Aliases and keep you safe from phishing emails. Email address search allows you to see within seconds who owns an Email Address, their Full Name, Current Address, Social Media Profiles, Phone number(s), Photos, and more.
Performing a reverse email lookup by yourself is a lengthy and daunting process. That is why you can take a shortcut and perform email search online, through professional websites like RecordsFinder. In this case, your search can take you further, connecting you to legit public records nationwide. You can find people's real name, contact information, criminal records and much more, so you can protect yourself and your loved ones.
Why Choose RecordsFinder.com?

Fast
Search over 2 billion records instantly. Easily find the information you are looking for with three easy steps- search, sign up, and view report.

Comprehensive
We have one of the most comprehensive data coverages in the industry including state, federal, county, municipal, and private data sources when available.

Affordable
With our unlimited search access, you can look up as many reports as you want! Others charge for every single search.

Reliable
Millions of users rely on us to deliver accurate and current data for their information needs.
Search Email Ownership on RecordsFinder.com
The information on this website is taken from records made available by state and local law enforcement departments, courts, city and town halls, and other public and private sources. You may be shocked by the information found in your search reports. Please search responsibly.
Recordsfinder.com is not a “consumer reporting agency” and does not supply “consumer reports” as those terms are defined by the Fair Credit Reporting Act (FCRA). Pursuant to our Terms of Service and Privacy Policy, you acknowledge and agree not to use any information gathered through Recordsfinder.com for any purpose under the FCRA, including but not limited to evaluating eligibility for personal credit, insurance, employment, or tenancy.
Searches of license plate and VIN information are available only for purposes authorized by the Driver’s Privacy Protection Act of 1994 (DPPA).
By clicking “I Agree” you consent to our Terms of Service, agree not to use the information provided by Recordsfinder.com for any unlawful purposes, and you understand that we cannot confirm that information provided below is accurate or complete.
The search you are about to conduct on this website is a people search to find initial results of the search subject. You understand that any search reports offered from this website will only be generated with the purchase of the report or account registration.

